Home/PCIDSS
PCIDSS
PCIDSS
PCI DSS: Everything You Need to Know!
In today’s digital age, the security of payment card data is more critical than ever.
The Payment Card Industry Data Security Standard (PCI DSS) was established to tackle the increasing threat of data breaches and the subsequent financial losses experienced for businesses and consumers. Before the advent of PCI DSS, major credit card companies like Visa, MasterCard, American Express, Discover, and JCB each had their own security protocols, leading to confusion and inconsistency. PCI DSS unifies these efforts under a single, comprehensive framework designed to protect cardholder data and enhance global security standards.
A Brief Overview of PCI Compliance
The PCI DSS is a globally recognized set of security standards that are designed to ensure that all entities that accept, process, store, or transmit credit card information maintain a secure environment. Introduced in 2006 by the Payment Card Industry Security Standards Council (PCI SSC), PCI DSS was created to address the rising threat of credit card fraud and data breaches, while providing a framework for securing cardholder data and fostering consumer confidence.
PCI is the family of security standards that is intended to secure the processing infrastructure of the payment industry.
The PCI Standards are tailored for three communities
- Merchant and Processors
- Software Developers
- Manufactures
Payment Card Industry Security Standards
Protection Of Cardholder Payment Data
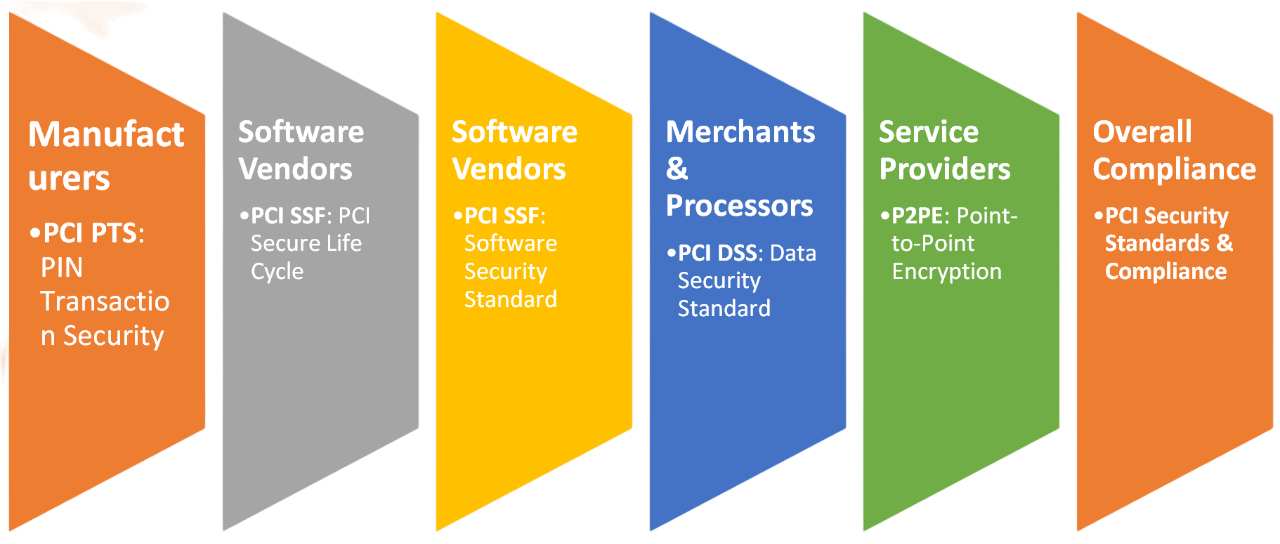
Overview of Different Standards
Sr. No. | Standard | Description |
1 | PCI DSS (Payment Card Industry Data Security Standard) | PCI DSS covers security of the environments that store, process, or transmit account data. The scope of PCI DSS covers environments receiving account data from payment applications and other sources—acquirers, for example. |
2 | PCI SSF = PCI Secure SLC + PCI Secure Software (Payment Card Industry Software Security Framework) | PCI Secure SLC covers the validation of mature secure software lifecycle management practices in place to ensure protection of payment transactions and data, minimize vulnerabilities, and defend against attacks. |
PCI Secure Software covers validation of payment software product designed, developed, and maintained in a manner that protects payment transactions and data, minimizes vulnerabilities, and defends against attacks. | ||
3 | PCI PTS – POI (Payment Card Industry PIN Transaction Security Point of Interaction) | The PCI PTS – POI standard covers device tamper detection, cryptographic processes, and other mechanisms used to protect the PIN and other sensitive data, such as cryptographic keys. |
4 | PCI PTS – PIN (Payment Card Industry PIN Transaction Security – Personal Identification Number) | The PCI PTS – PIN standard covers secure management, processing and transmission of personal identification number (PIN) data during online and offline payment card transaction processing. |
5 | PCI PTS – HSM (Payment Card Industry PIN Transaction Security – Hardware Security Module) | The PCI PTS – HSM standard covers the design of hardware security modules and for securely protecting those devices until they are deployed. |
6 | PCI P2PE (Payment Card Industry Point-to-Point Encryption) | PCI P2PE (Point-to-Point Encryption) covers secure encryption, decryption, and key management for point-to-point encryption solutions. Requirements for a P2PE solution will vary depending on the deployment environment and the technologies used for a specific implementation. |
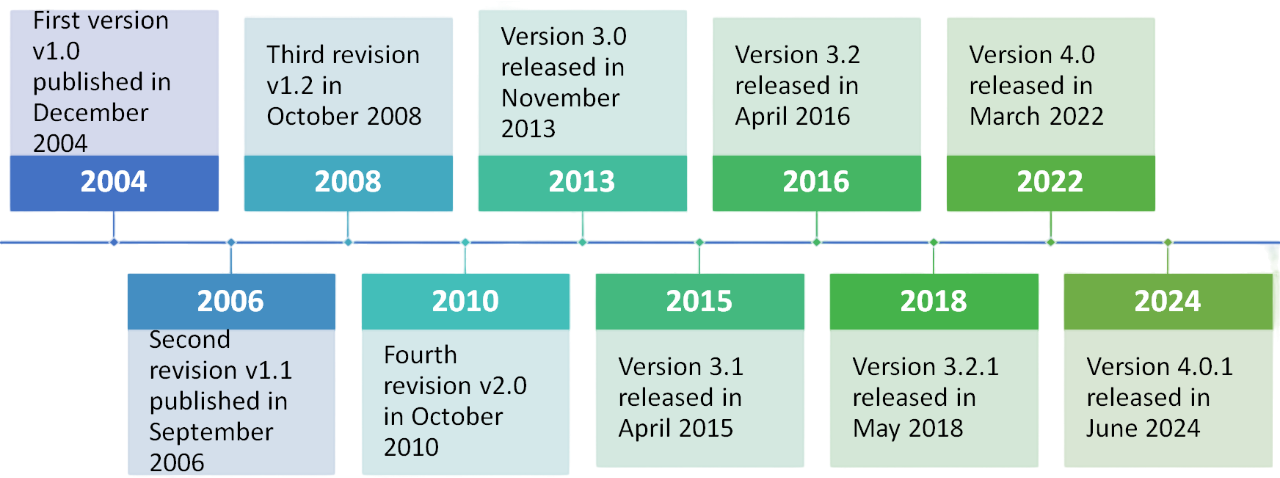
History of PCI DSS
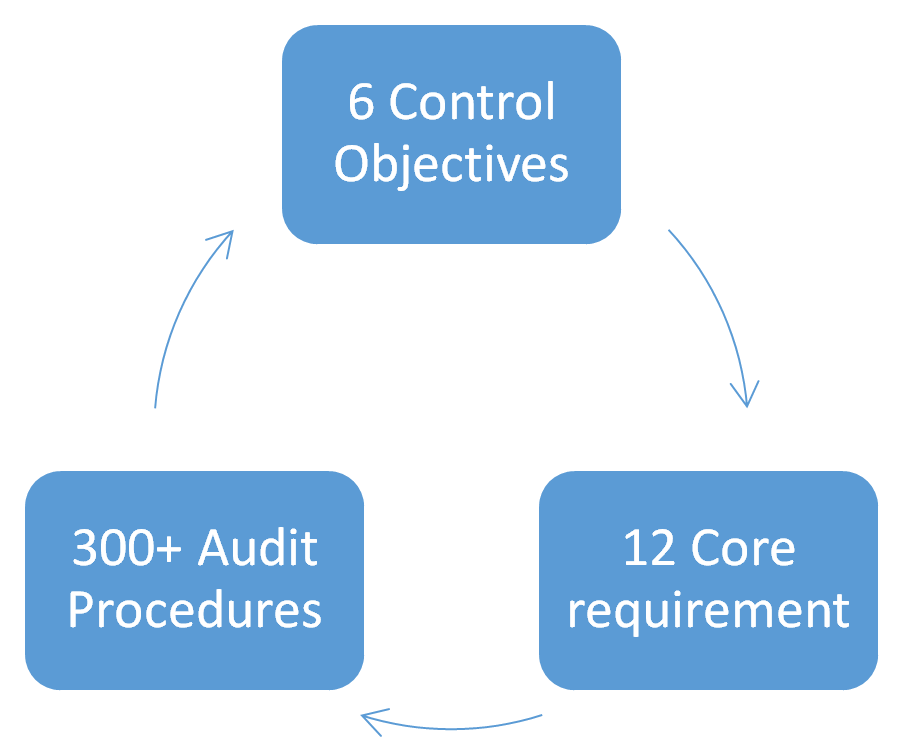
The Requirements of PCI DSS
Organizations need to understand that the requirements set forth by the PCI DSS are both operational and technical, and the core focus of these regulations is always to protect cardholder data.
Typically, there are 12 requirements of PCI DSS 4.0, and these include:
Control Objective | PCI DSS 4.0 Requirements |
Build and Maintain a Secure Network and Systems | 1. Install and maintain network security controls. |
2. Apply secure configurations to all system components. | |
Protect Account Data | 3. Protect stored account data. |
4. Protect cardholder data with strong cryptography during transmission over open public networks. | |
Maintain a Vulnerability Management Program | 5. Protect all systems and networks from malicious software. |
6. Develop and maintain secure systems and software. | |
Implement Strong Access Control Measures | 7. Restrict access to system components and cardholder data by business need to know. |
8. Identify users and authenticate access to system components. | |
9. Restrict physical access to cardholder data. | |
Regularly Monitor and Test Networks | 10. Log and monitor all access to system components and cardholder data. |
11. Test security of systems and networks regularly. | |
Maintain an Information Security Policy | 12. Support information security with organizational policies and programs. |
PCI DSS V4.0 Structure
Benefits of PCI DSS Compliance
There are several benefits of PCI DSS Compliance that organizations can avail in terms of protecting data and enhancing their reputation as security-conscious organizations. Some of them are listed as follows:
- Builds customer trust by securing cardholder data, fostering loyalty and repeat business.
- Minimizes data breach risks, reducing potential costs like fines, legal fees, and reputational damage.
- Prevents and detects fraud, lowering financial loss risks.
- Shows adherence to industry best practices, enhancing reputation with partners and regulators.
Need to Know the PCI DSS Compliance Best Practices?
Well, although PCI DSS is vital for organizations dealing with cardholder information, the compliance process is also challenging for businesses. For one, the requirements for PCI DSS cover an extensive range of security controls that are more than intricate for businesses to understand and implement. Especially for SMEs with limited resources, maintaining and complying with PCI DSS security systems, competencies, and processes can be cost-intensive as it requires ongoing monitoring, testing, and updating of security measures. However, with cybersecurity consulting from the professionals at Sysatek, businesses can make their IT infrastructure management easy and ensure vulnerability testing doesn’t have any pitfalls.
Address
4th Floor, Bizness Square, Hitex road, HITEC city, Madhapur, Hyderabad, Telangana 500084, IN
Phone
+91 80085 14034
info@sysatek.com
© Copyrights Sysatek.com 2026, All Rights Reserved.

